
Eduroam - Wireless (Wifi) Network
Eduroam is the WIFI network at DCU
DCU students and staff must configure and connect all digital devices to the secure encrypted eduroam WiFi Network. Access to the eduroam network is authenticated through your DCU account.
Eduroam provides secure and easy to use WiFi access in thousands of locations in more than a hundred countries. This page provides a step-by-step guide on how to access eduroam. Please follow the specific instructions for your device.
Once you’ve connected for the first time, you'll never need to enter your details again on that device, eduroam will automatically connect you whenever you’re in range of an eduroam hotspot. The hotspot you’re using never sees your credentials.
Please Note: If you change your main password you MUST remove the current eduroam profile and run the tool again to ensure you have a working/secure wireless internet connection on Campus
Please note: You should never configure an eduroam connection manually, only the options below are fully secure.
Connect your Laptop to Eduroam by clicking on the button below.
- Go to https://www.dcu.ie/iss/eduroam-wireless-wifi-network
- Scroll down and click on “Eduroam Click Here”
- Click on “Click here to download your eduroam® installer”
- Select the organisation Dublin City University.
- Enter your DCU credentials as follows yourusername@ad.dcu.ie followed by your DCU password twice.
- *Remember to sign in with your username, not your email address*
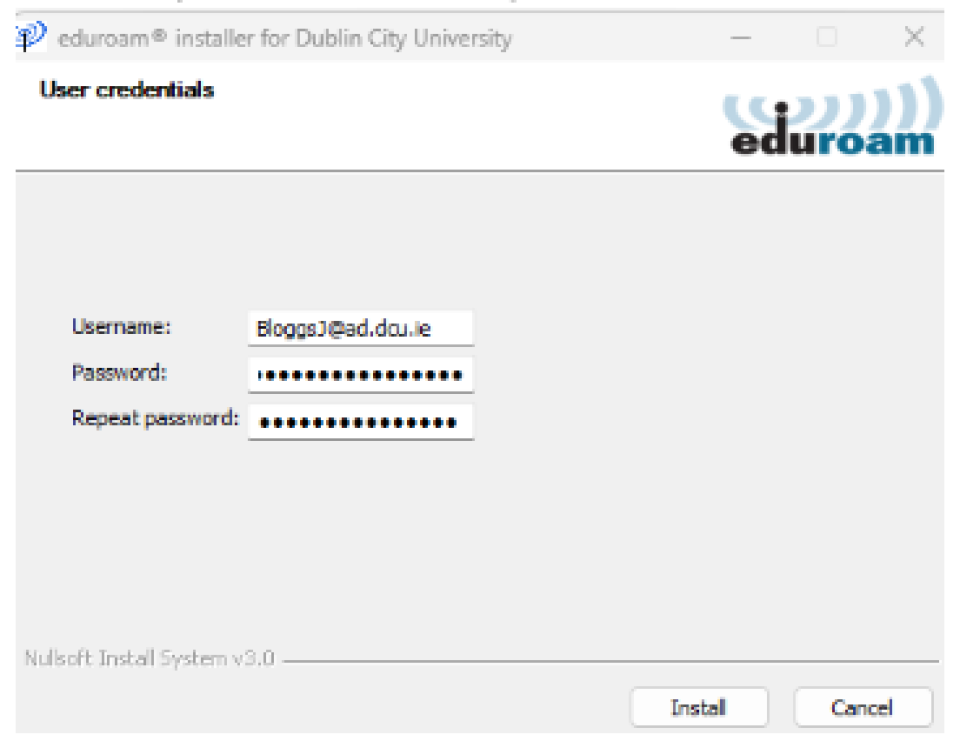
This is how you should log into Eduroam Cat Installer
- Click Install and let the installer run, click Finish.
- Go to the Wi-Fi connections and connect on Eduroam.
- Go to https://www.dcu.ie/iss/eduroam-wireless-wifi-network
- Scroll down and click on “Eduroam Click Here”
- Click on “Click here to download your eduroam® installer”.
- Select the organisation Dublin City University.
- Click on eduroam, this will download the eduroam cat installer.
- Click on the Apple logo top-left and click on system preferences. (As seen below)
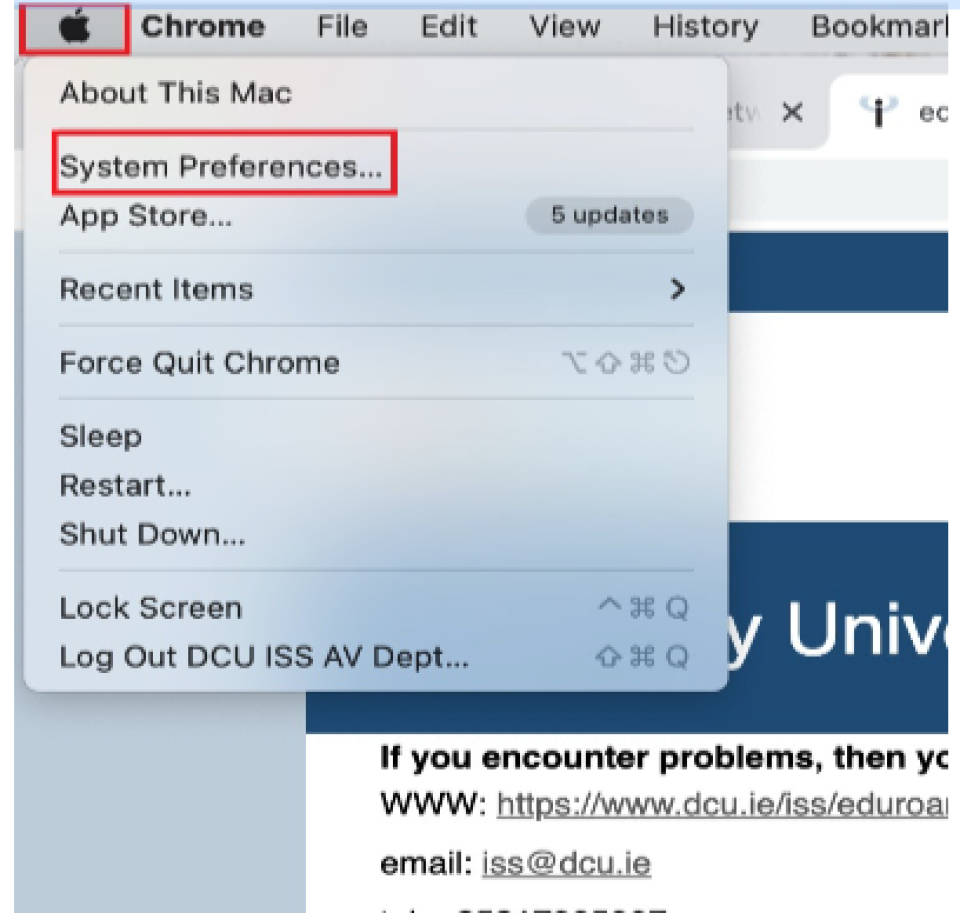
System Preferences
- Click on Profiles (bottom right-hand corner as seen below).
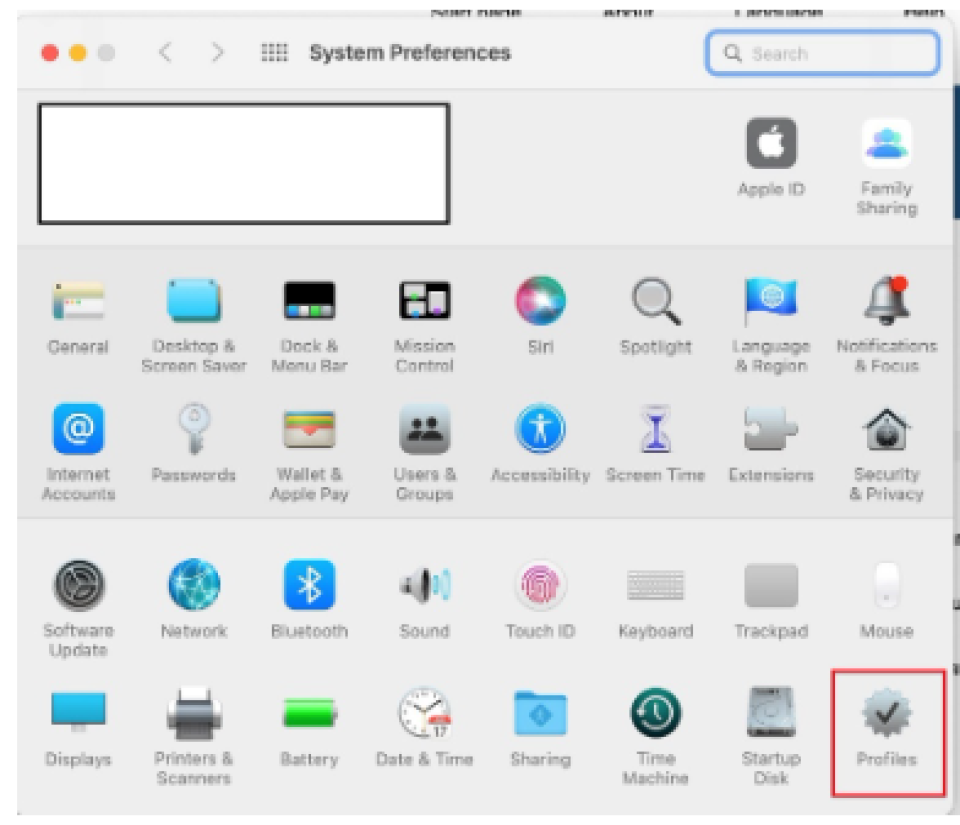
Profiles
- Click on Install (As seen below).
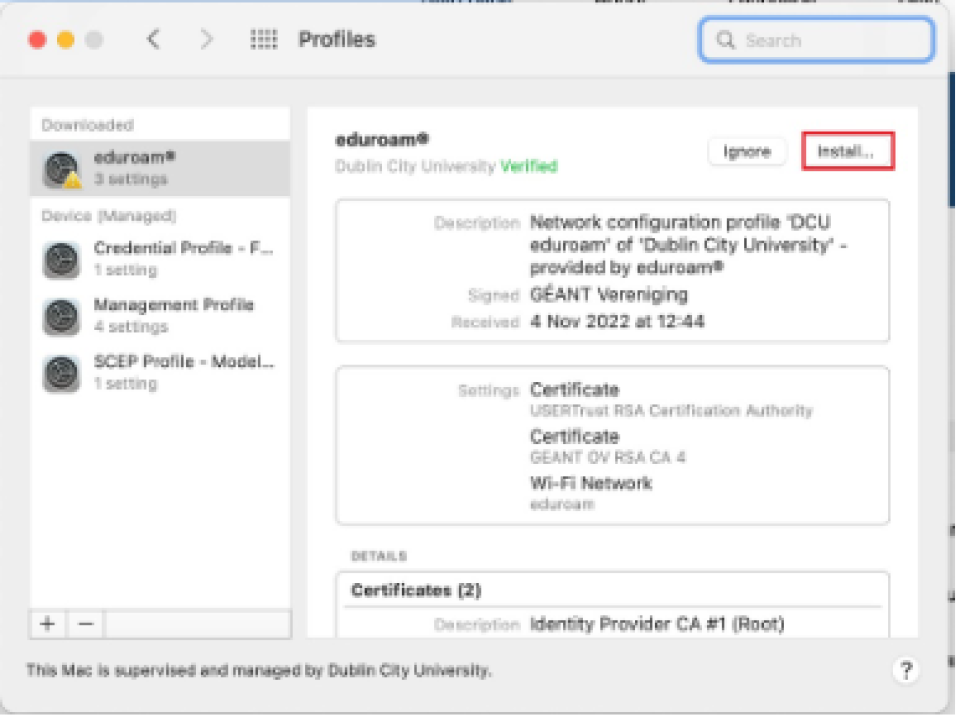
Install Eduroam
- Login with your DCU username followed by @ad.dcu.ie and your DCU password.
*Remember to sign in with your username, not your email address*
For example
Username: BloggsJ@ad.dcu.ie
Password: **************** - Sign in with Apple ID if prompted, click allow to join Eduroam if prompted.
- Click on the Wi-Fi logo (top right-hand corner) and click on eduroam to join.
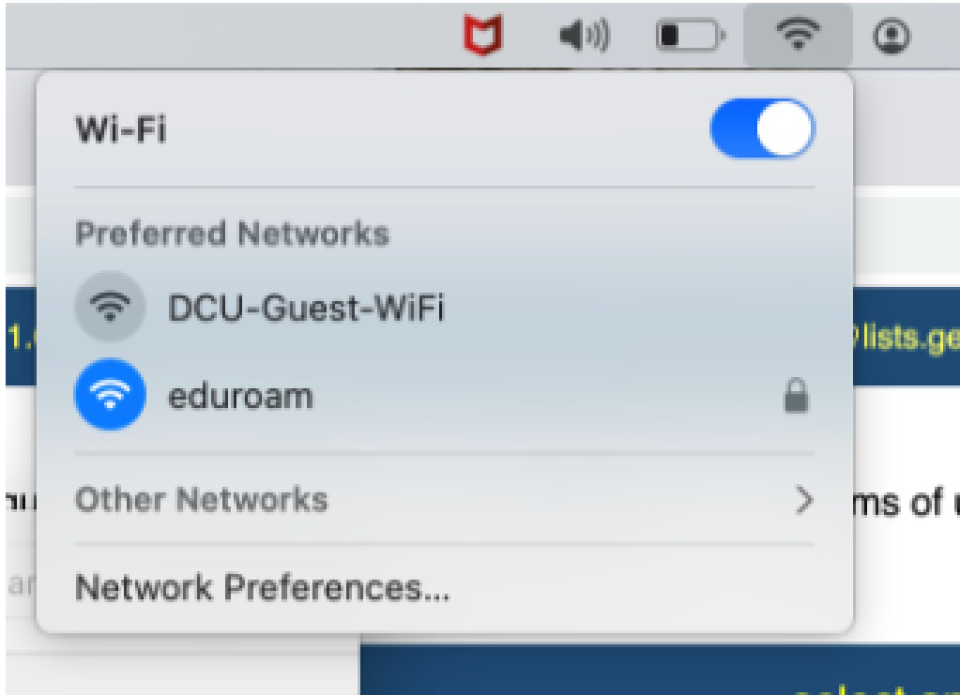
Select Eduroam
Terms and Conditions
This service (DCU-Guest Wifi) is provided for short-term use only by guests to the DCU campuses.
Please be aware that: The DCU code of conduct and policies linked within apply to the use of this service.
This is an unsecured network and should only be used for basic web browsing purposes.
This service is only for guests who are unable to use DCU’s main wifi service - Eduroam.
This is a limited service that only allows basic browsing and SSL-VPN (ports 80, 443)
DCU Staff and Students
DCU staff and students are advised to use our main Wifi service - Eduroam. DCU-Guest Wifi is an unsecured network and should not be used for University business purposes.
Please do not access your DCU accounts from the guest network.
Eduroam Registered Guests
DCU Eduroam Wifi service is also available to visiting staff and students who were registered and configured with the Eduroam service at their home institution before arriving at DCU.
Please contact your home institution if you wish to configure this service for the first time.
Additional Eduroam Information
Eduroam (Educational Roaming) implements a wireless infrastructure that facilitates roaming educational users to gain wireless Internet access at other member sites.
Access Eduroam is authenticated - always using your credentials from your home institution regardless of where you access the service. The wireless network name is the same in all places - "Eduroam".
Eduroam Usage Policy
The following policies govern the use of the Eduroam service:
The most notable part of the Eduroam policy is Section 6, which is indicated here:
- A user's role is, in principle, always a visitor who wants Internet access at a Server Provider (SP).
The user MUST abide by their IdP's (Identity Provider) AUP or equivalent and respect the visited organisation's AUP or equivalent.
Where regulations differ, the more restrictive applies.
Users MUST, as a minimum, abide by relevant law of the country where (s)he is physically situated while using the service, home or abroad. - The user is responsible for taking reasonable steps to ensure that they are connected to a genuine Eduroam service (as directed by their home organisation) before entering their login credentials. The primary means to achieve this is to validate the server certificate presented to the user upon login.
- The user is responsible for their credentials and the use of any service they might provide.
- If credentials are compromised, the user MUST immediately report to their IdP (home institution).
- The user is obliged to inform the SP (where possible) and IdP of any faults with the eduroam service.
Policy compliance:
If a user breaches these acceptable usage policies, the following actions will be taken:
The user will be suspended from the service.
Examples of a breach of the AUP include any activity that may adversely affect the quality of the WiFi service or impact the reputation of the University. Serious violations, e.g. infringing on copyright, may result in disciplinary action being taken by the University.
Network traffic is passively monitored, and details are logged for incident response purposes only.
Protocols allowed on DCU Eduroam service:
DCU complies with the complete list of allowed ports and protocols as suggested by the Eduroam policy. There may also be a range of additional protocols allowed, over and above those stated as a requirement by Eduroam.
Currently, the Eduroam service in DCU does not support IPv6.
Advice for DCU staff and students visiting other Eduroam institutions
- Test that Eduroam works for you in DCU before you leave. If you can't get it working here, you're likely to have problems elsewhere as well.
- Search for (and read) any documentation the remote site has on Eduroam before you leave. Forewarned is forearmed, and sites might have some variations in how it is implemented.
- The remote site may use different network security settings to those used in DCU (e.g.WPA2 TKIP AES). If so, you will need to change that part of your network configuration.
- The authentication part of the configuration is specific to the home institution (DCU), so you shouldn't change it. It includes the EAP methods (Microsoft protected EAP EAP-TTLS-PAP and PEAP+MSCHAPv2, certificates and server verification. Do not change any of those.
Useful links:
Support Contact Details:
DCU students and staff must configure and connect all digital devices only to the secure encrypted Eduroam WiFi Network. Access to the eduroam wireless network is authenticated using your DCU account and provides secure and easy WiFi access in thousands of locations in more than a hundred countries.
Once you’ve connected for the first time, you'll never need to enter your details again on that device, eduroam will automatically connect you whenever you’re in range of an eduroam hotspot. The hotspot you’re using never sees your credentials.
Please note: You should not configure an eduroam connection manually, only the ‘geteduroam’ app is fully secure for Android devices.
Connect your Android device to Eduroam, follow the instructions below:
Please ensure that your device is at least Android 8.0 or later
- When you are on a DCU campus, on your Android phone / tablet, slide down from the top of the screen to open 'Wi-Fi’ networks and press and hold on the eduroam network. If it says ‘Forget Network’, press this to remove the old connection.
-
Connect to ‘DCU Guest Wifi’ or your 4G/5G connection and open the link below or search for "geteduroam" in the Play store. Click ‘Install’.
-
Click ‘Open’
-
Type ‘DCU’ in the Institution box and select ‘Dublin City University’ from the list of institutions and click ‘Next’.
-
Enter your DCU account as username@ad.dcu.ie, not your email address and password in the boxes and click ‘Connect to Network’.
-
Enter your DCU username and password in the boxes and click ‘Connect to Network’.
-
On the final page, click ‘Ok’.
-
Check the wireless network listed on your Android device to confirm that you are now connected to ‘eduroam’.
More detailed instructions are available to view here.
Please note: Android powered devices are produced by a variety of manufacturers, each of which may customise the interface in a different manner. As such, the instructions above may not exactly match your device. There are also several different versions of the Android operating system available that may also lead to deviations from the above steps.
If you have a previously installed version of the ‘eduroam CAT’ or ‘geteduroam’ app on your Android device and are experiencing issues, you will need to uninstall the app, delete the eduroam network and complete the steps as outlined above once again.
DCU students and staff must configure and connect all digital devices only to the secure encrypted Eduroam WiFi Network. Access to the eduroam wireless network is authenticated using your DCU account and provides secure and easy WiFi access in thousands of locations in more than a hundred countries.
Once you’ve connected for the first time, you'll never need to enter your details again on that device, eduroam will automatically connect you whenever you’re in range of an eduroam hotspot. The hotspot you’re using never sees your credentials.
Please note: You should not configure an eduroam connection manually, only the ‘geteduroam’ app is fully secure for IOS devices.
Connect your IOS device to Eduroam, follow the instructions below:
Please ensure that your device is at least iOS 11.0 or later.
- When you are on a DCU campus, on your IOS phone / tablet, slide down from the top of the screen to open 'Wi-Fi’ networks and press and hold on the eduroam network. If it says ‘Forget Network’, press this to remove the old connection.
-
Connect to ‘DCU Guest Wifi’ or your 4G/5G connection and open the link below or search for "geteduroam" in the Play store. Click ‘Install’.
-
Click ‘Open’
-
Type ‘DCU’ in the Institution box and select ‘Dublin City University’ from the list of institutions and click ‘Next’.
-
Enter your DCU account as username@ad.dcu.ie, not your email address and password in the boxes and click ‘Connect to Network’.
-
On the final page, click ‘Ok’.
-
Check the wireless network listed on your IOS device to confirm that you are now connected to ‘eduroam’.
More detailed instructions are available to view here.
Please note: If you have a previously installed version of the ‘eduroam CAT’ or ‘geteduroam’ app on your iOS device and are experiencing issues, you will need to uninstall the app, delete the eduroam network and complete the steps as outlined above once again.




